Critical Infrastructure Research · 2025 · KIT OCI
German Telehealth Infrastructure: Structural Mapping for Threat Modeling
A KIT doctoral researcher needed a structural baseline before she could model cybersecurity risk in German hospital networks. I mapped three digitised care delivery architectures to give her that foundation under the EU NIS2 framework.
Research questions
Three questions for the threat model
- Architecture: How are systems connected, and where do data dependencies concentrate?
- Criticality: Which operations are time-critical, and what does disruption cost clinically?
- Regulatory exposure: Which operators carry NIS2/KRITIS obligations, and how does that shape their architecture?
In healthcare, IT availability is a clinical metric. Disruption is measured in minutes, and the consequence is measured in neurological damage, not just data loss.
Network architectures
Three integration models, three structural profiles
Three models, each representing a distinct integration strategy: vertical, horizontal, and networked. Scope limited to regional care delivery networks. The national TI, gematik, and ePA layers are excluded.
Vertical Integration
Horizontal Community Integration
Regional Network Coordination
Structural comparison
Security-relevant dimensions across the three models
| Dimension | PORT Stuttgart | PORT Hohenstein | NEVAS Bavaria |
|---|---|---|---|
| Integration type | Vertical — hospital campus | Horizontal — community multi-agency | Regional hub-and-spoke network |
| Network nodes | 1 center + RBK hospital campus | 13 departments + county agencies | 19 hospitals (3 hubs + 16 spokes) |
| Population served | ~22,500 | ~3,700 | 2.9 million |
| Time-criticality | Moderate — chronic care coordination | Low — scheduled primary care | Extreme — stroke "golden hour" |
| Data sensitivity | Ambulatory + inpatient EHR convergence | Multi-disciplinary community records | Acute neurological + imaging data |
| External connections | Bosch Health Campus research network | County health office, public agencies | 19 inter-hospital video/data links |
| NIS2 exposure (indicative) | Likely essential entity (via RBK hospital, subject to NIS2UmsuCG thresholds) | Likely important entity (subject to operator size thresholds) | Likely essential entity (subject to formal classification) |
| Structural concern (literature-indicated) | Research network boundary | Rural IT resource constraints (ENISA 2023) | 16 spoke hospitals with variable IT maturity (ENISA 2023) |
| Active since | 2022 | September 2019 | 2014 |
NEVAS Bavaria — structurally most complex
A 19-hospital network where availability is a patient safety constraint
NEVAS connects 3 stroke centers with 16 regional hospitals via 24/7 video and data links. Regional hospitals lack round-the-clock neurologists. Remote experts fill that gap during the critical "golden hour."
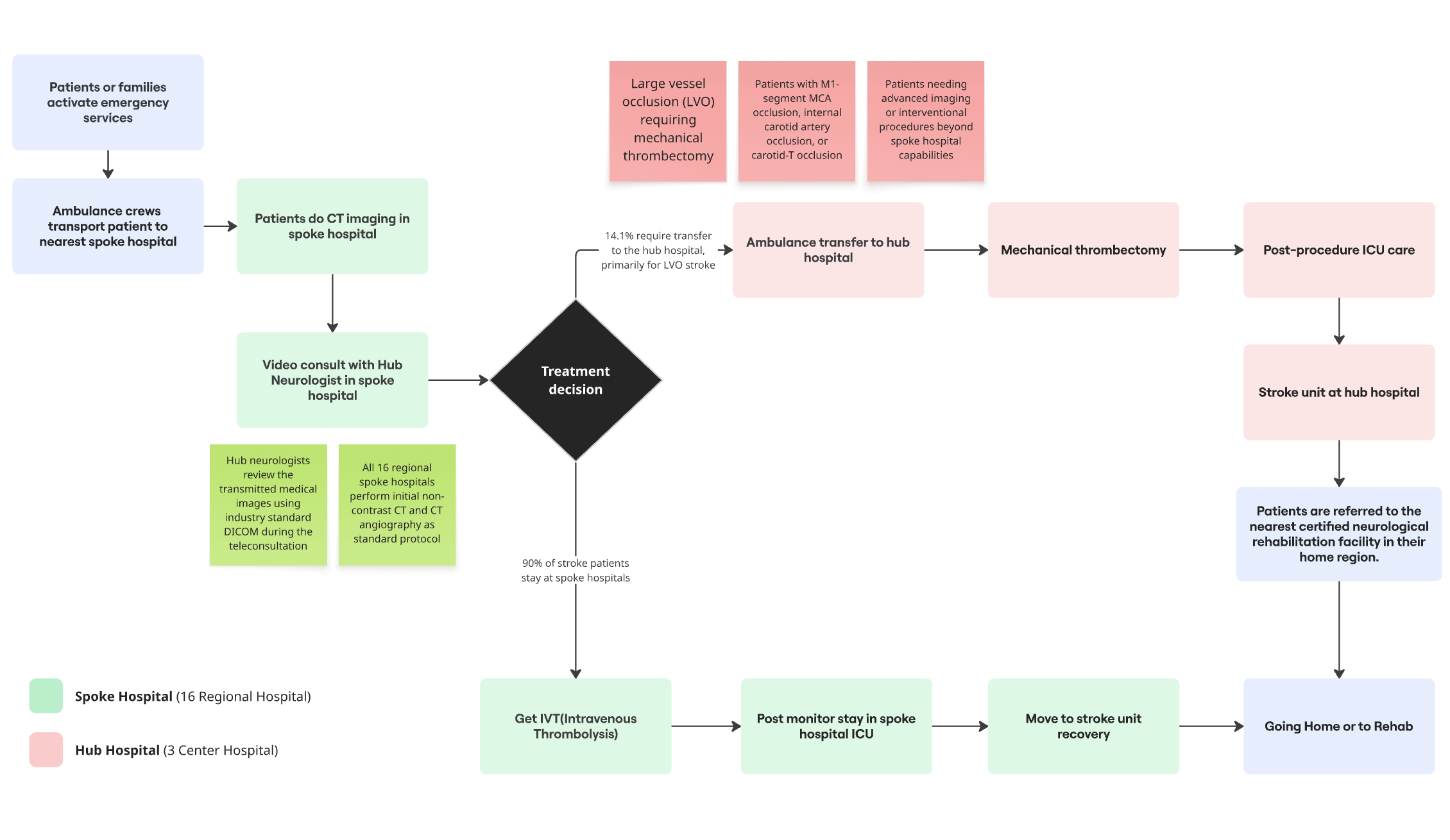
Three structural characteristics matter most for threat modeling:
PORT Stuttgart — research network exposure
Hospital campus integration with an external research boundary
PORT Stuttgart sits inside Robert Bosch Hospital and connects to the Bosch Health Campus research ecosystem. Structurally, this creates a dual-domain environment: KRITIS-governed clinical operations alongside a research network with different security standards.
PORT Hohenstein — rural security maturity gap
Cross-agency data sharing in a resource-constrained environment
PORT Hohenstein serves ~3,700 people across 13 departments and integrates with county agencies including long-term care coordination and the county health office. Multiple entities access health records in an environment with limited IT security resources.
Structural observations
What the mapping identified as relevant for threat modeling
Integration architecture shapes the structural preconditions for security risk
Vertical integration (PORT Stuttgart) concentrates connectivity at the campus boundary. Horizontal integration (PORT Hohenstein) distributes access across agencies with varying IT resources. Network coordination (NEVAS) creates interconnection across 19 IT environments. Threat modeling needs to be architecture-specific.
Availability outranks confidentiality in time-critical networks
Standard frameworks prioritise CIA in that order. In stroke networks like NEVAS, availability is paramount. A ransomware attack causing 6-hour downtime during a stroke event has immediate, irreversible clinical consequences. Different from administrative systems.
Spoke hospitals in distributed networks warrant further security assessment
In NEVAS, the 16 spoke hospitals are the most numerous interconnection points. ENISA's 2023 report identifies smaller facilities as generally having lower IT security maturity across Europe. Whether that holds for NEVAS specifically is an open question for the doctoral researcher's subsequent assessment.
NIS2 entity classification depends on operator-specific thresholds
NIS2 classifies healthcare as essential, but entity classification under Germany's NIS2UmsuCG depends on operator-specific criteria (turnover, employee count). The structural differences between models are relevant context, but formal classification was outside this mapping's scope.
Implications for the OCI research
A baseline that enables the right questions
This was scoped as infrastructure mapping, not security assessment. The researcher needed to know what is connected, what is time-critical, and what is regulated before applying her security framework.
The deliverable gives her three things: a typology of network architectures for scoping threat models, a mapping of NIS2 entity obligations per operator, and identification of NEVAS as the highest-priority case where availability risk and life-safety consequences converge.
Scope limitations. Literature-based and descriptive. Not a security assessment, penetration test, or formal threat model. Risk badges reflect structural characteristics, not validated ratings from STRIDE or OCTAVE. The national TI, gematik, and ePA are excluded. Actual protocols, authentication mechanisms, and segmentation architectures remain open questions for fieldwork.
This pattern (diverse architectures, variable security maturity, harmonised NIS2 obligations) is not unique to Germany. It is how healthcare digitalisation has proceeded across the EU: driven by clinical need, not security design.
Sources & References
- Masouris et al. (2024) — Telemedical Stroke Care, NEVAS network
- Gesundheitszentrum Hohenstein — PORT primary care center
- Bosch Health Campus — PORT Stuttgart context
- NEVAS network — SAGE Journals
- PORT Gesundheitszentrum — Hausarztpraxis
- PORT Gesundheitszentrum — Bosch Health Campus
- Community Health Nursing — Bosch Health Campus
- NEVAS DSG Certification — LMU Klinikum
- PMC — Integrated Care Models in Germany
- ENISA (2023) — Health Sector Threat Landscape Report, European Union Agency for Cybersecurity
- EU Directive 2022/2555 (NIS2) — measures for a high common level of cybersecurity across the Union
- BSI (2022) — IT-Grundschutz für Krankenhaus-Informationssysteme, Bundesamt für Sicherheit in der Informationstechnik